- Joined
- Oct 2, 2004
- Runs
- 218,165
https://www.ft.com/content/e96924f0-3722-11e7-99bd-13beb0903fa3
Hackers responsible for the wave of cyber attacks that struck organisations across the globe on Friday from the UK’s National Health Service to European telecoms giant Telefonica used tools stolen from the US National Security Agency, the Financial Times has been learned.
An exploit known as “eternal blue”, developed by US spies has been weaponised by the hackers to super-charge an existing form of ransomware known as WannaCry, three senior cyber security analysts said. Their reading of events was confirmed by western security officials who are still scrambling to contain the spread of the attack.
Ransomware is a form of malware which locks victims out of their own computers by encrypting files on them and demands a ransom - typically payable in the untraceable digital currency bitcoin - in order to return access. Infection is almost always made by email.
The latest version of WannaCrypt spread laterally through the computer networks of infected organsiations, however. The NSA’s eternal blue exploit allows the malware to spread through file-sharing protocols set up across organisations - many of which span the globe.
Security officials in the UK, which has been among the countries worst hit, currently believe the attacks are the work of a criminal group - though they are still working to assess the full nature of the attack. The UK’s National Cyber Security Centre, an arm of GCHQ, has been put into a state of high-alert. The speed and virulence of the infection has caught many by surprise.
NHS hospitals across the UK were hit by the attack with medical staff confronted with messages demanding payment to unlock access to data.
The UK was one of several countries, including Spain and Portugal, where computer systems in various sectors were infiltrated by the same ransomware.
NHS Digital, the arm of the UK health service co-ordinating a response, said “a number” of NHS organisations had been affected by a ransomware attack, “which is affecting a number of different organisations”.
It said that there was no evidence that patient data had been accessed but was continuing to assess the damage done by the hack.
Downing Street said that the prime minister was being kept updated and that Jeremy Hunt, the health secretary, was being briefed by the NCSC.
Dominic Grieve, chair of the intelligence and security committee, told the Financial Times that the government was not complacent about the threat from hackers. “The government has already allocated a colossal amount of resources to this . . . but you can’t have 100 per cent guarantee that you cannot be hacked into.”
In October, Ben Gummer, Cabinet Office minister, warned that “large quantities of sensitive data” held by the NHS and government were being targeted by hackers — with the potential to disrupt Britain’s energy, water and transport networks.
The same or a similar virus was used in a large-scale attack in Spain on Friday that hit companies including Telefónica, the country’s main telecoms provider. Telefónica said that it had suffered a “cyber security incident” affecting the personal computers of “some” employees.
It is not known if the attacks in Spain and on the NHS are connected. In Portugal, a spokesman for the police cybercrime unit told local media that “large-scale” ransomeware attacks had hit a number of Portuguese firms, particularly communication operators.
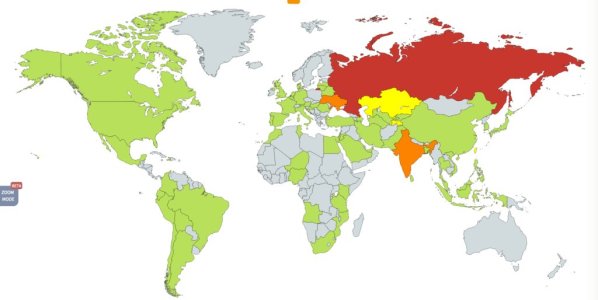
There have been unverified reports of cyber attacks in several other countries, including Russia.
The hackers are thought to have deployed a virulent version of ransomware known as WannaCry. Typically, hackers will seek to infect IT systems with ransomware in order to demand money to “unlock” the affected computers.
Barts Hospital, in central London, confirmed that it was among the hospitals to have been hit and said it had been forced to cancel routine appointments and divert ambulances to neighbouring hospitals as the “major IT disruption” took hold. It asked the public “to use other NHS services wherever possible” and said that the IT breakdown was causing delays at all the hospitals within the trust.
“We have activated our major incident plan to make sure we can maintain the safety and welfare of patients,” it added. The switchboard had been affected at Newham Hospital in east London but direct-line phones were still working.
At the hospital in London, technicians were turning away patients seeking blood tests and the electronic sign that determines the queue was switched off. “It’s because of the computers,” one staffer told a confused woman.
One person said that managers at all levels were in meetings to assess the attacks.
A doctor working in a hospital in east London affected by the attack said staff had “turned everything off and we are sitting back and going on seeing patients as we normally do”. Staff had reverted to paper records, he added.
East and North Hertfordshire NHS Trust posted a statement on its website to say it was “currently experiencing significant problems with our IT and telephone network which we’re trying to resolve as soon as possible”. Hospital trusts and GP groups in Lancashire were also reporting problems.
NHS Digital said it was “working closely with the National Cyber Security Centre, the Department of Health and NHS England to support affected organisations and to recommend appropriate mitigations”.
Vanessa Sandhu, a GP in Braintree, Essex, said: “We got a call from the CCG [Clinical Commissioning Groups] saying there had been a security breach. We all had to shut down our computers and unplug all cables from the walls.
“It was scary — we had no idea what was going on. We didn’t have access to our notes or patient medical records. We couldn’t request blood tests or ultrasounds. We had to disconnect the surgery telephones so we couldn’t communicate with other doctors or patients. We tried to see the patients in the building, but everyone else we told to go home.
“We’ve had to close the surgery for the day. Some hospitals have had to shut down so it’s going to be absolute carnage in A&E if you can’t do emergency tests or get blood results for those most in need.”
Hackers responsible for the wave of cyber attacks that struck organisations across the globe on Friday from the UK’s National Health Service to European telecoms giant Telefonica used tools stolen from the US National Security Agency, the Financial Times has been learned.
An exploit known as “eternal blue”, developed by US spies has been weaponised by the hackers to super-charge an existing form of ransomware known as WannaCry, three senior cyber security analysts said. Their reading of events was confirmed by western security officials who are still scrambling to contain the spread of the attack.
Ransomware is a form of malware which locks victims out of their own computers by encrypting files on them and demands a ransom - typically payable in the untraceable digital currency bitcoin - in order to return access. Infection is almost always made by email.
The latest version of WannaCrypt spread laterally through the computer networks of infected organsiations, however. The NSA’s eternal blue exploit allows the malware to spread through file-sharing protocols set up across organisations - many of which span the globe.
Security officials in the UK, which has been among the countries worst hit, currently believe the attacks are the work of a criminal group - though they are still working to assess the full nature of the attack. The UK’s National Cyber Security Centre, an arm of GCHQ, has been put into a state of high-alert. The speed and virulence of the infection has caught many by surprise.
NHS hospitals across the UK were hit by the attack with medical staff confronted with messages demanding payment to unlock access to data.
The UK was one of several countries, including Spain and Portugal, where computer systems in various sectors were infiltrated by the same ransomware.
NHS Digital, the arm of the UK health service co-ordinating a response, said “a number” of NHS organisations had been affected by a ransomware attack, “which is affecting a number of different organisations”.
It said that there was no evidence that patient data had been accessed but was continuing to assess the damage done by the hack.
Downing Street said that the prime minister was being kept updated and that Jeremy Hunt, the health secretary, was being briefed by the NCSC.
Dominic Grieve, chair of the intelligence and security committee, told the Financial Times that the government was not complacent about the threat from hackers. “The government has already allocated a colossal amount of resources to this . . . but you can’t have 100 per cent guarantee that you cannot be hacked into.”
In October, Ben Gummer, Cabinet Office minister, warned that “large quantities of sensitive data” held by the NHS and government were being targeted by hackers — with the potential to disrupt Britain’s energy, water and transport networks.
The same or a similar virus was used in a large-scale attack in Spain on Friday that hit companies including Telefónica, the country’s main telecoms provider. Telefónica said that it had suffered a “cyber security incident” affecting the personal computers of “some” employees.
It is not known if the attacks in Spain and on the NHS are connected. In Portugal, a spokesman for the police cybercrime unit told local media that “large-scale” ransomeware attacks had hit a number of Portuguese firms, particularly communication operators.
There have been unverified reports of cyber attacks in several other countries, including Russia.
The hackers are thought to have deployed a virulent version of ransomware known as WannaCry. Typically, hackers will seek to infect IT systems with ransomware in order to demand money to “unlock” the affected computers.
Barts Hospital, in central London, confirmed that it was among the hospitals to have been hit and said it had been forced to cancel routine appointments and divert ambulances to neighbouring hospitals as the “major IT disruption” took hold. It asked the public “to use other NHS services wherever possible” and said that the IT breakdown was causing delays at all the hospitals within the trust.
“We have activated our major incident plan to make sure we can maintain the safety and welfare of patients,” it added. The switchboard had been affected at Newham Hospital in east London but direct-line phones were still working.
At the hospital in London, technicians were turning away patients seeking blood tests and the electronic sign that determines the queue was switched off. “It’s because of the computers,” one staffer told a confused woman.
One person said that managers at all levels were in meetings to assess the attacks.
A doctor working in a hospital in east London affected by the attack said staff had “turned everything off and we are sitting back and going on seeing patients as we normally do”. Staff had reverted to paper records, he added.
East and North Hertfordshire NHS Trust posted a statement on its website to say it was “currently experiencing significant problems with our IT and telephone network which we’re trying to resolve as soon as possible”. Hospital trusts and GP groups in Lancashire were also reporting problems.
NHS Digital said it was “working closely with the National Cyber Security Centre, the Department of Health and NHS England to support affected organisations and to recommend appropriate mitigations”.
Vanessa Sandhu, a GP in Braintree, Essex, said: “We got a call from the CCG [Clinical Commissioning Groups] saying there had been a security breach. We all had to shut down our computers and unplug all cables from the walls.
“It was scary — we had no idea what was going on. We didn’t have access to our notes or patient medical records. We couldn’t request blood tests or ultrasounds. We had to disconnect the surgery telephones so we couldn’t communicate with other doctors or patients. We tried to see the patients in the building, but everyone else we told to go home.
“We’ve had to close the surgery for the day. Some hospitals have had to shut down so it’s going to be absolute carnage in A&E if you can’t do emergency tests or get blood results for those most in need.”